Mullvad VPN
Review: Mullvad VPN and VPN guide
A privacy respecting VPN.
TL;DR
Mullvad VPN
Super OK!
A VPN should do four things. One, not peek into your traffic. Two, actually respect your privacy. Mullvad's VPN is the only one that I've seen that actually fulfills both. Mullvad is the best for privacy but may lack features you may want, and the trade-off is for you to make.
Review
Before we begin, I want to re-emphasize our editorial standards, specifically the section about not having affiliate links. This will be important as we continue with the rest of the review.
Secondly, this will be a combination of a high level guide on VPNs in general, what they do, what are some possible reasons for using one, and why we consider Mullvad, specifically, so highly.
If you want to skip the VPN explainer and go directly to the review, jump down to the Mullvad section.
What is a VPN?
You may have seen your favorite YouTuber or other media influencer begin their mid-roll ad break by going "This video was sponsored by <insert company here> VPN!" So what is a VPN?
A VPN is a Virtual Private Network. It's a term used in networking that describes, generally, a secure way to connect a network enabled device to another network. The other network can be on the internet, it could be at home, it could be at the office, but the important part is that this network is not where you are currently connected to. Many corporate networks have VPN set up in a way that allows you to connect your company issued phone or laptop to the company network, without having to expose the entire company infrastructure to the rest of the internet.
Well, that's great, but sounds basically nothing like what these advertisements talk about. So what exactly, then, are all of these VPN companies trying to sell you?
Commercial VPNs
For the purposes of this review, we'll define a commercial VPN as any VPN service, either free or paid, that allows you to connect to its infrastructure in order to access web resources elsewhere. It should not provided by the company you work for, or be set up yourself.
Commercial VPNs are extremely profitable, at least in terms of margin. All you need to do is to buy/rent rack space in a co-location facility, slap some VPN software on it, and buy a 10 Gigabit line to the outside internet. Done. Repeat in as many geographic areas as possible. Hey, too lazy to rent out server space want to make even more money? Simply white-label someone else's service and call it your own! In this example, though, Mozilla actually does white-label Mullvad, but your money goes to Mozilla first.
Why use a commercial VPN?
There are many legitimate reasons why you may want to use a VPN. Maybe you want to prevent your browsing activity and network activity from being seen from your ISP (they are known to be sneaky). Maybe your threat profile involves blending in your web traffic with a lot of other people. Maybe it's to prevent websites or other internet users from knowing your IP address (a good thing if websites block IPs by country, or preventing harassment from other users online [eg. a DDoS attack]). After all, buying an IP address from another company is easier than finding a data center and doing it yourself.
Why not use a commercial VPN?
This is entirely dependent on your threat profile. Are you someone that travels a lot for work? Do you travel to places where using a VPN is suspicious or illegal? Do you download lots of Linux ISOs? Do you do a lot of online banking? These are all factors to consider before hitting that connect button.
Trust
Ultimately the decision to pick a commercial VPN provider comes down to how much you trust them. After doing a lot of reading and digging, I've found that basically all of them are completely untrustworthy. Information is difficult to come by on the internet, and most of it is clouded by blogspam looking for a quick affiliate buck, or have had it's integrity compromised by being a review website owned by the company operating the VPNs.
Claims
Just to parrot some of the claims that I hear from the ad copy given to YouTubers to read, many of them use scare tactics (keep yourself safe from hackers!) or misrepresenting the service (prevent your ISP from viewing your browsing history!) These are obvious ploys to get you to purchase their service, but there's actually issues with both of the two examples I picked.
First, the claim about hackers makes no sense, at least in the current year of 2023. Over 90% of all web browsing is now over HTTPS, and the old school method of just watching packets on the network for login credentials is not trivial nowadays due to the prevalence of encryption. Of course, if a website is designed very poorly, this can still happen, and a VPN will not help you (and could hurt you).
Second, the claim about preventing your ISP from viewing your browsing history is also problematic. It's not false, as at face value, it's true that your current ISP can't see what sites you visit (I won't bother explaining how DNS works here), but by using a commercial VPN, you've now turned that company into your new ISP. Is that really any better?
Another common one is hiding your IP address. While this can reveal your home address, it's usually using some lookup service like MaxMind which got it's data set from who-knows-where and correlated with your general (or specific) address using who-knows-how, which is sketchy in it's own right, for sure. This is actually not a claim I'll refute, but as you'll see below, the way that companies can do this may not be entirely kosher.
Infrastructure
They say the internet runs on a series of tubes. Wild, I know. But, that tube infrastructure is only as secure as we say it is.
One of the issues with commercial VPNs (and this is true even for Mullvad), is that you, the end user, are entirely reliant on the infrastructure provider to both have 1) secured their infrastructure in a way that prevents bad actors from seeing your traffic and that 2) other users in the infrastructure are ALSO not able to see your traffic.
The issue here being that it's entirely their word against yours. You have no (reasonable) way of verifying their claims yourself, and they have no obligation to let you. The providers sometimes do use outside third-parties to audit their infrastructure, but you enter the next layer of having to trust this third-party company, particularly if it's a company you have never heard of or aren't familiar with.
Residential Proxies
One of the primary selling points of a commercial VPN is being able to view geofenced content (eg. a show not available in your country on a streaming service). Have you ever considered what it would take to make that work?
Most streaming services actually BLOCK data center/co-location IP ranges because of this issue, but many companies will tout the ability to get around this restriction. Preventing CAPTCHAs are another.
Dovetailing with the concept of infrastructure, many, MANY VPN companies are actually owned by "residential proxy" services. Tesonet is one example with several notable brands in it's portfolio such as Nord Security (of NordVPN fame), Surfshark (of Surfshark VPN fame), and oxylabs (web scraping/residential proxy service). Kape Technologies (note: provided by Windscribe VPN, I'm only using it because it has sources in it) is all sorts of sketchy, with a history in browser hijacking, and a series of umbrella aquisitions (PrivateInternetAccess, ExpressVPN, and several VPN review sites). Bright Data (formerly known as Luminati Networks) also provides web scraping services, a residential proxy, and huh, a free VPN. Coincidence? There are many more such examples (notice how even with the thorough research provided, there's an affiliate link at the end of the article?).
These services are shady enough as is - what the heck is a web scraping service? How are they getting legitimate residential addresses? The answer can vary from legitimate (end users knowingly install their client - I am having a hard time finding a case where this is true, gee, I wonder why...), to sketchy (end users unknowingly install the client bundled or built in with some other software during installation), to illegitimate (end users unknowingly have the software installed somewhere on their network). But it's this SAME network of residential accounts that allow for YOU, the commercial VPN customer to show up say, in the UK, to watch, say The Office. You're simply (more likely than not) unknowingly appearing out of someone else's house, and they are (more likely than not) unknowingly letting you. Does this sound like being a Tor exit node operator? That's because it, for all intents and purposes, is.
Logging
This is something that is extremely difficult to prove for ANY commercial VPN. Many will claim that they don't log user requests. Some may word it in a way that still allows them to collect SOME user data. Some say they don't and then turn around and provide logs anyway. Some may straight up lie. However, only VPN services which have 1) received a legal request for information 2) disclosed the required information and 3) disclose that they received a legal request (see: warrant canary) could potentially be trusted, and even then that's still taking their word for it.
Affiliates
One of the reasons that okrevie.ws goes out of its way to remove affiliate links from products we talk about is that if I'm reading or watching a review, and there's an affiliate link, of course your goal as an influencer would to be to try to get as many people as possible to click or purchase the product, because that's how you get more money.
And that, inherently, is untrustworthy. How can I take your word for it when you, the influencer, have likely received the product for free, and also get a cut of sales? Mullvad, specifically, does not have an affiliate program, and you'd be hard pressed to find another commercial VPN service that does not.
Setting up your own
This is burying the lede, but honestly, I use my home hosted VPN way more than I do Mullvad. Why? For all of the reasons on trust above. I control all of the hardware on my side of the cable modem for the service that I pay for. I run my own DNS server and do not rely on my ISP to resolve websites for me. But this is highly technical, and not everyone knows how to do this, and for that, it's easy to recommend a service that will do it for you, assuming, of course, you do trust them.
Trust and safety, again
Many VPN ad copies recommend you do sensitive work such as banking through their VPN. DO NOT DO THIS, EVER. For and and all of the reasons listed above. Before doing sensitive work, you should consider your threat profile, and mitigation is entirely dependent on where you are and what you need. There are situations where mobile data is more secure, there are situations where a home VPN is better. There are situations where mobile data is the LEAST secure, and there are situations where you have no choice but to use a commercial provider. You an also mix and match, for example, using your home VPN on a mobile connection.
Mullvad
After all those words on VPNs, let's talk about Mullvad.
Advantages
There are a couple of really nice features to using Mullvad.
Wireguard support
Wireguard is a super cool, lightweight, up and coming VPN tunnel protocol that is so good that it's already been merged into the Linux kernel (Linus Torvalds himself thinks it's a work of art).
Anecdotally, Wireguard is super easy to set up (it's what I use in my own setup), easier to set up than OpenVPN, and is faster than OpenVPN. So, I'm very pleased that Mullvad supports it. Of course, if you still prefer OpenVPN or SOCKS proxy configurations, they support those too.
Pro-tip: if you have a GL.iNet router, you can add your account number directly to the router and not have to set up Wireguard yourself (this will eat into one of your device slots)
Privacy respecting payment
Mullvad is the first service, or website, that I've seen, where the most information that they require from you is, basically nothing - no email, no password. Upon payment through their payment processor, you get assigned an account number, and from then on, that's the number you use to connect to their infrastructure and add money to. That's it.
You can add money to the account for up to a year at a time, and when the money runs out, your connections stop working. This is so anonymous that they literally accept an envelope of cash as payment. You can also just share your account number with other people, and other people can even top up your account. Subscriptions are not supported, in fact, they have been removed.
Transparency
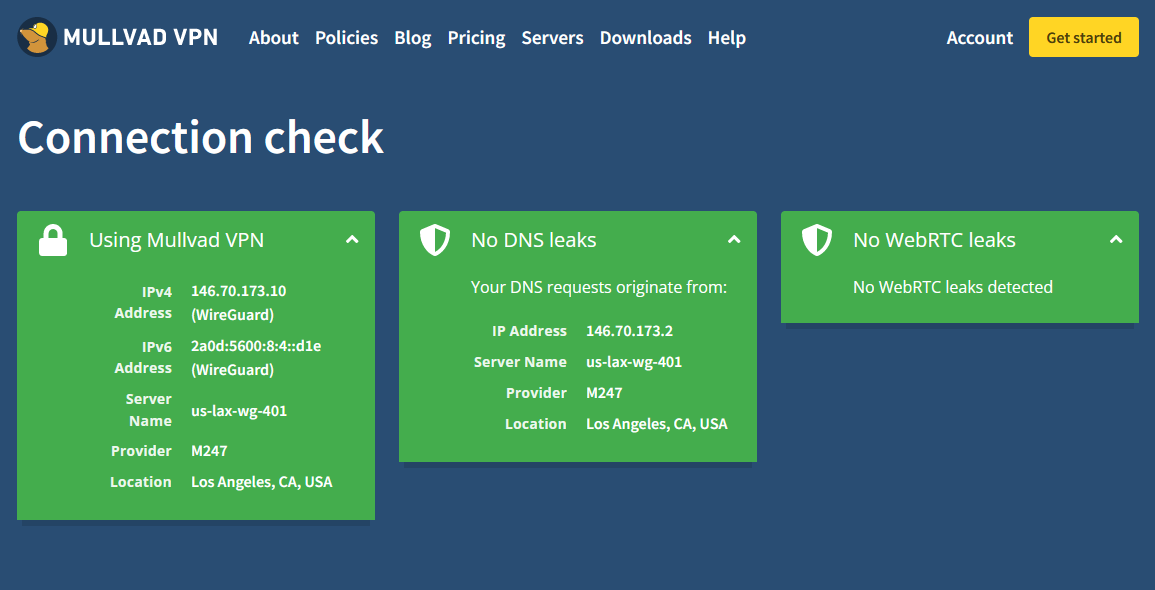
This is of course, calling back to the previous point about trusting their word, but they have taken a lot of steps to improve privacy in many unexpected ways. Diskless infrastructure is a particularly interesting technical challenge, and responding to a search warrant is interesting, if not uneventful (uneventful is good).
Other features
Don't want to set up Wireguard yourself? No problem, just use their app! Just as a heads up, each installation (phone, computer) does eat into your 5 device slots, so I prefer the Wireguard solution. However, if it's just you, your computer, and your phone, that's probably a pretty good solution for any.
I just saw this post, but Tailscale integration seems super cool for people who are also using Tailscale.
And, the previously mentioned GL.iNet router support, of course.
Disadvantages
There are some downsides, and for some, this may be a dealbreaker.
Geo-restriction support
As we discussed above in the section on trust, being able to access geo-locked content (TV shows, movies) rely on a questionably willing network of residential computers in other countries. Mullvad only provides servers in data centers, which are very easy to be blocked by content providers, due to all traffic originating from the same location, usually.
"Fourteen Eyes"
Allegedly, there is an international cooperation for collection of information, for which Sweden (where Mullvad is headquartered) is supposedly a part of. My arguement though, is are your non-cooperative country VPN services...more trustworthy? Who's to say. But it's a point that privacy advocates will be sure to point out.
Summary
Mullvad, for what it is, which is a commercial VPN provider with heavy emphasis on privacy, is the best recommendation that I have for VPNs. For those looking to watch content not available in your country, this is probably not the one for you due to the lack of using residential proxies, and in that case I would advise you to use your money wisely if you pick another option.